USB attacks explained (Krzysztof Opasiak, LVEE-2017) — различия между версиями
Материал из 0x1.tv
StasFomin (обсуждение | вклад) |
StasFomin (обсуждение | вклад) |
||
== Thesis ==
{{LinksSection}}
* [https://lvee.org/ru/abstracts/243 Talks page]
<!-- <blockquote>[©]</blockquote> -->
{{fblink|1933723420214003}}
{{vklink|711}}
<references/>
[[File:{{#setmainimage:USB attacks explained (Krzysztof Opasiak, LVEE-2017)!.jpg}}|center|640px]]
{{stats|disqus_comments=0|refresh_time=2019-05-08T01:38:488-19T20:42:59.74200719|vimeo_comments=0|vimeo_plays=43|youtube_comments=0|youtube_plays=467}}
[[Категория:Linux]]
[[Категория:LVEE-2017]]
[[Категория:Информационная безопасность]] | |||
Версия 17:43, 19 августа 2019
- Speaker
- Krzysztof Opasiak
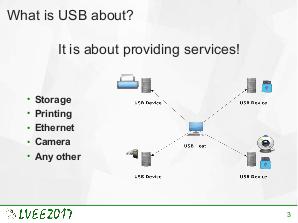
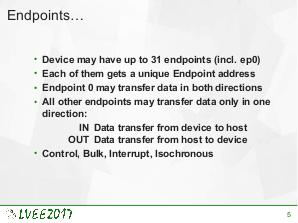
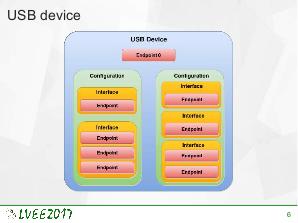
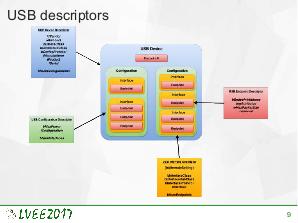
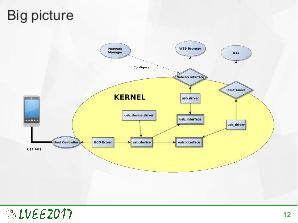
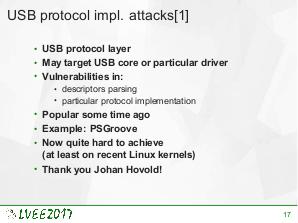
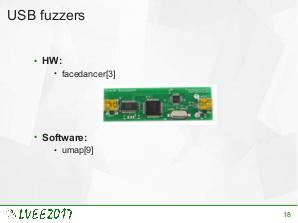
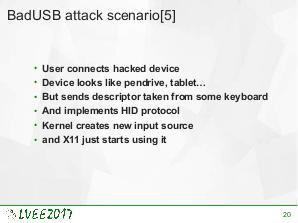
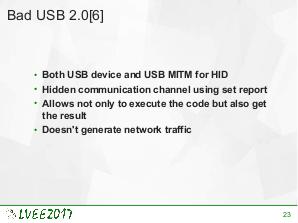
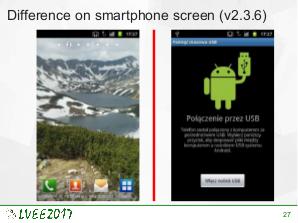
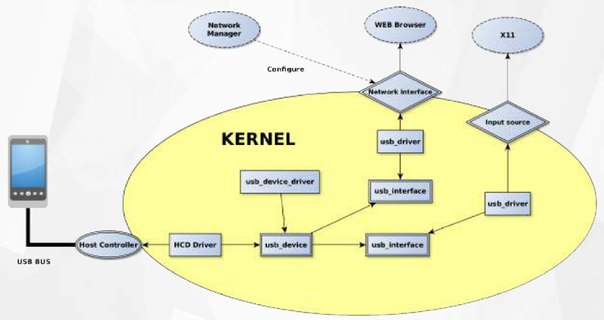
USB is the most common external interface in the world. Even machines which, for security reasons, are disconnected from the Internet often offer USB connectivity. This creates a new attacks surface for skilled hackers. USB implementation may be exploited on various levels. To effectively protect against such attack, knowledge about already exploited vulnerabilities is required. This paper is a survey of state-of-the-art USB-related attacks.
Video
Посмотрели доклад? Понравился? Напишите комментарий! Не согласны? Тем более напишите.
Slides
Thesis
Links
Plays:90
Comments:0